RPKI Adoption Is Accelerating: Is Your IP Data Keeping Up?

Get Unlimited Access to IPinfo Lite
Start using accurate IP data for cybersecurity, compliance, and personalization—no limits, no cost.
Sign up for freeIn February 2026, Sparkle (AS6762), a global Tier-1 transit provider, began rejecting RPKI-invalid prefixes. They joined Bell Canada, Deutsche Telekom, and a growing list of major networks that no longer just flag invalid routes: they drop them entirely.
This is more than a gradual best-practice adoption, it's an infrastructure shift. And it changes what IP intelligence needs to tell you.
For anyone unfamiliar with RPKI, Cloudflare's Is BGP Safe Yet? is one of the clearest resources out there. It tracks which networks have deployed Route Origin Validation (ROV) and explains why it matters. In short: RPKI is a cryptographic framework that lets network operators prove they're authorized to announce a given IP prefix. Without it, BGP (the protocol that routes all internet traffic) operates on trust alone.
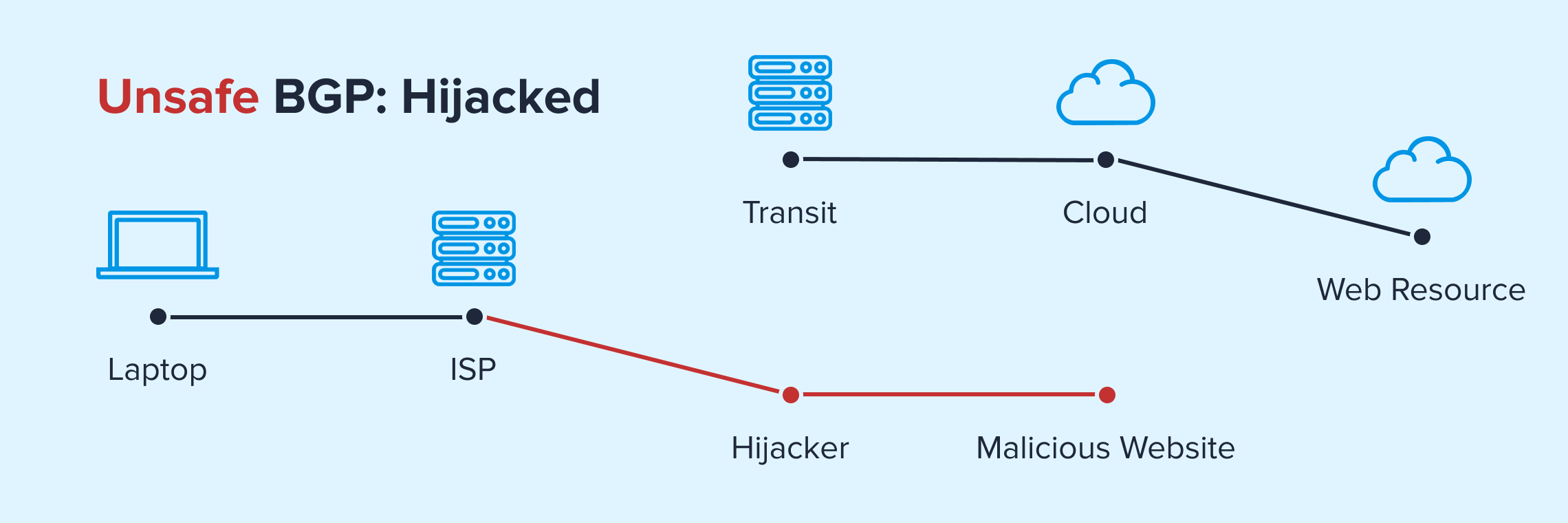
That trust is easily exploited. In a BGP hijack, a malicious or misconfigured network announces someone else's IP prefix as its own and without RPKI validation, other networks have no way to tell the difference. Traffic gets silently rerouted to the wrong destination, enabling anything from service outages to data interception.
The Counterintuitive Risk of Partial Adoption
Here's what makes the current moment interesting and underappreciated.
As RPKI enforcement spreads unevenly, a new class of risk is emerging. Research published by APNIC ahead of NDSS 2026 showed that partial ROV deployment is making certain BGP hijacks harder to detect, not easier. In these "stealthy hijacks," a victim's routing tables look perfectly normal, their ROV-enabled neighbors correctly drop the invalid announcement, but traffic is silently diverted through legacy networks that don't perform validation.
The result: the control plane says everything is fine while the data plane tells a different story. The networks that haven't adopted ROV become the blind spots that attackers or even accidental misconfigurations can exploit.
This means RPKI validation status isn't just useful for routing engineers tuning BGP policies. It's becoming essential context for anyone analyzing IP traffic, investigating suspicious activity, or assessing infrastructure risk.
From Routing Hygiene to Operational Risk Visibility
We're seeing this firsthand. Enterprise network and security teams are increasingly looking to enrich their traffic flow data with RPKI validation status, not just for routing hygiene, but for operational risk visibility. The questions they're asking go well beyond traditional BGP monitoring: detecting trends in invalid vs. valid route usage, measuring what percentage of traffic flows over ROA-validated paths, flagging risk from potential route hijacks or leaks, and understanding how much of their traffic could break if the networks they depend on start dropping invalid routes, as more providers already are.
For organizations processing large volumes of traffic, an RPKI-invalid route that gets dropped by an enforcing network means real outages and real business impact. The shift from "best practice" to "enforcement" turns RPKI status from a routing team metric into an infrastructure-wide risk signal.
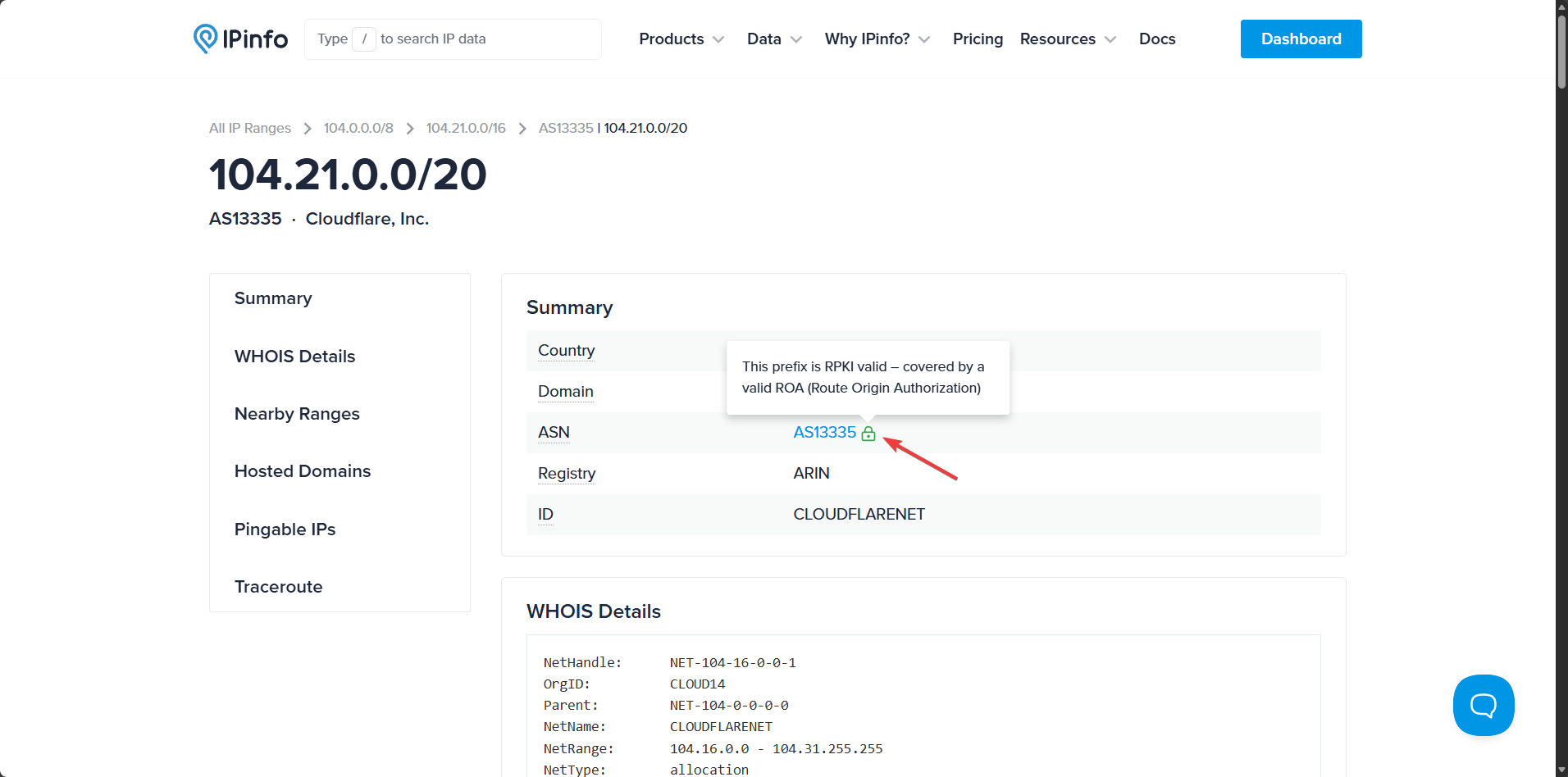
What's telling is who's paying attention. When we announced RPKI validation on our lookup pages, the response came not just from the network engineering community, but from security and infrastructure teams who hadn't previously engaged with routing data. That cross-audience interest signals something important: routing trust is no longer a niche concern.
Legacy IP Intelligence Describes the Internet as It Claims to Be
Legacy IP intelligence has historically worked by aggregating what the internet says about itself. Registry data, WHOIS records, routing tables… these sources tell you which ASN announces a prefix, what organization is behind it, and where the traffic should be going. That descriptive layer was sufficient when the primary question was attribution: who is behind this IP?
But as enforcement tightens and RPKI-invalid routes carry real operational consequences like dropped traffic, unreachable services, and degraded connectivity, knowing what the internet claims is no longer enough. You need to know whether those claims check out.
Measuring and Verifying, Not Just Describing
At IPinfo, we've always approached IP data differently. Our methodology is built on active measurement and evidence. We don't just mirror what registries say, we verify it against what we observe. RPKI validation fits naturally into that approach.
RPKI adds a cryptographic verification layer to routing data. It tells you who is announcing a prefix and whether they're authorized to. That's the difference between describing a claim and validating it.
We've started making this signal visible directly on our IP, Range, and ASN lookup pages. You can now see at a glance whether a route origin has been cryptographically verified, no separate validator tool required. Early feedback from our community confirms this is already replacing standalone validation workflows for many users. For full details on how this works, see our community announcement.
This is a first step. As routing security enforcement accelerates, validation signals like these will move from nice-to-have context to essential infrastructure insight.
The Bigger Picture
The internet is shifting from implicit trust to cryptographic verification, and IP intelligence needs to reflect that shift. As the gap between validated and unvalidated routes widens and as the operational consequences of landing on the wrong side of that gap grow, routing trust signals won't remain optional metadata. They'll be a critical context for security, fraud prevention, and infrastructure decisions.
We can fundamentally say that RPKI matters for IP analysis — but do your tools show it to you?
About the author

As the product marketing manager, Fernanda helps customers better understand how IPinfo products can serve their needs.