How VPNs and Residential Proxies Are Used in Abuse: Findings from 2026 RSAC Research
Get Unlimited Access to IPinfo Lite
Start using accurate IP data for cybersecurity, compliance, and personalization—no limits, no cost.
Sign up for freeAt RSA Conference 2026, we partnered with AbuseIPDB to share our new joint research analyzing over 260 million unique IPs, including 94M+ residential proxy IPs and 24M+ VPN IPs, to understand how anonymization infrastructure shapes real-world abuse.
We analyzed how VPNs and residential proxies intersect with real-world abuse, which types of attacks they're associated with, where they concentrate geographically, and how their infrastructure overlaps with confirmed botnets.
Below is a summary of the key findings. You can also watch the full presentation.
Our Data and Research Methodology
This research combined two perspectives:
- Reputation data from AbuseIPDB, based on their feeds of actively abusive IPs, built on crowdsourced reports validated through honeypot networks and reporter trust scoring
- Infrastructure context from IPinfo, built from evidence-based VPN detection, residential proxy detection, ASN, ISP, and geolocation data
We applied abuse thresholds (report count + confidence score), analyzed overlap between VPN, residential proxy, and abusive IPs, and segmented by provider, ASN/ISP, and geography.
We analyzed:
- 94M+ unique residential proxy IPs
- 24M+ unique VPN IPs
- Totaling 260M+ unique IPs observed across both datasets
We also layered in confirmed botnet infrastructure to ground the analysis in known malicious activity.
Abuse Concentrates in Anonymous Infrastructure
One finding stood out immediately:
53% of actively abusive IPs are associated with VPNs or residential proxies.
Within that:
- 45% are tied to residential proxies
- 41% of known botnet IPs overlap with residential proxy infrastructure
At the same time, abuse represents a small portion of the total IP population:
- ~3.75% of VPN IPs
- Just over 6% of residential proxy IPs
The signal here is concentration. When abuse occurs, it’s often associated with infrastructure designed to abstract identity and location.
VPNs and Residential Proxies Behave Differently
From an infrastructure perspective, these systems operate in very different ways.
VPNs: Longer-Lived Infrastructure, Less Abusive
VPN networks tend to be:
- Longer-lived
- Centrally operated
- More sensitive to reputation
- More persistent abuse
We also observed meaningful variation between providers. Some networks showed significantly higher associations with abuse than others. Among the top 15 VPN providers by abuse reports, the percentage of IPs appearing in AbuseIPDB ranged from as low as 5% to over 94%.
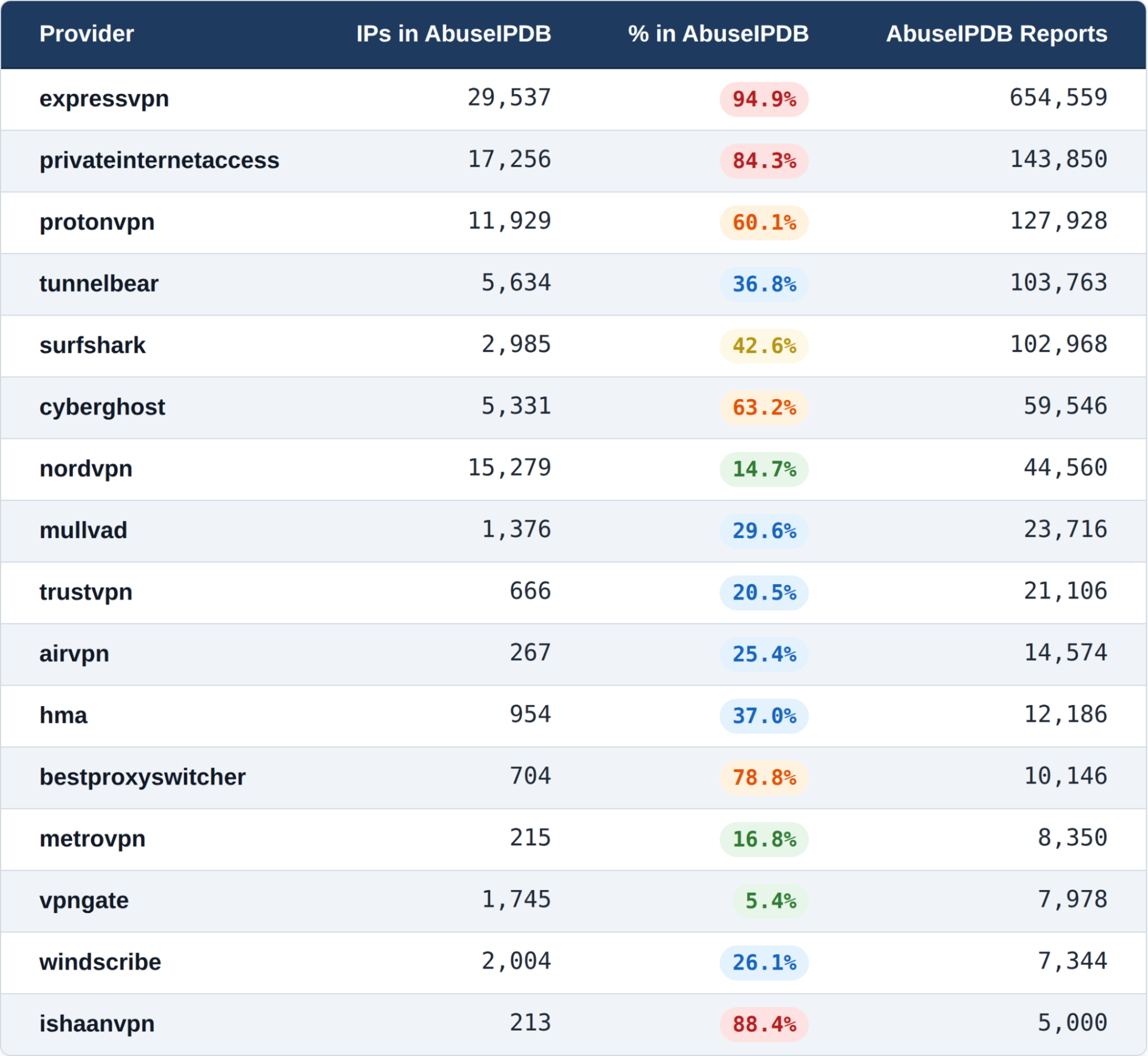
One likely factor is how IPs are allocated. When many users share a smaller pool of IPs, activity accumulates more quickly on those addresses.
Read our previous research report on VPNs.
Residential Proxies: More Ephemeral, More Abusive
Meanwhile, a significant percentage of abusive activity originates from residential proxies.
They have:
- Higher abuse percentages
- Higher churn
- Shorter lifecycles
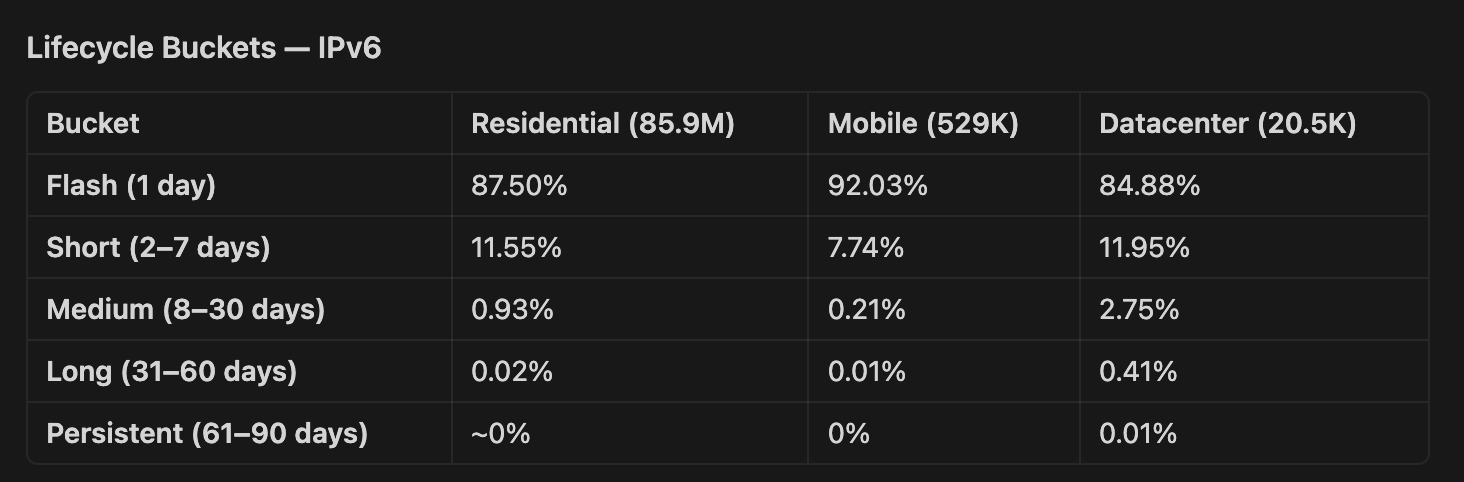
The lifecycle data makes this concrete. Among IPv4 residential proxies, roughly a third were active for only a single day and another 43% lasted less than a week, an average lifespan of approximately 7.8 days. IPv6 residential proxies were even more ephemeral: nearly 88% lasted just one day, with an average lifespan of 1.3 days. In a single month, we observed over 75 million confirmed residential proxy exit nodes.
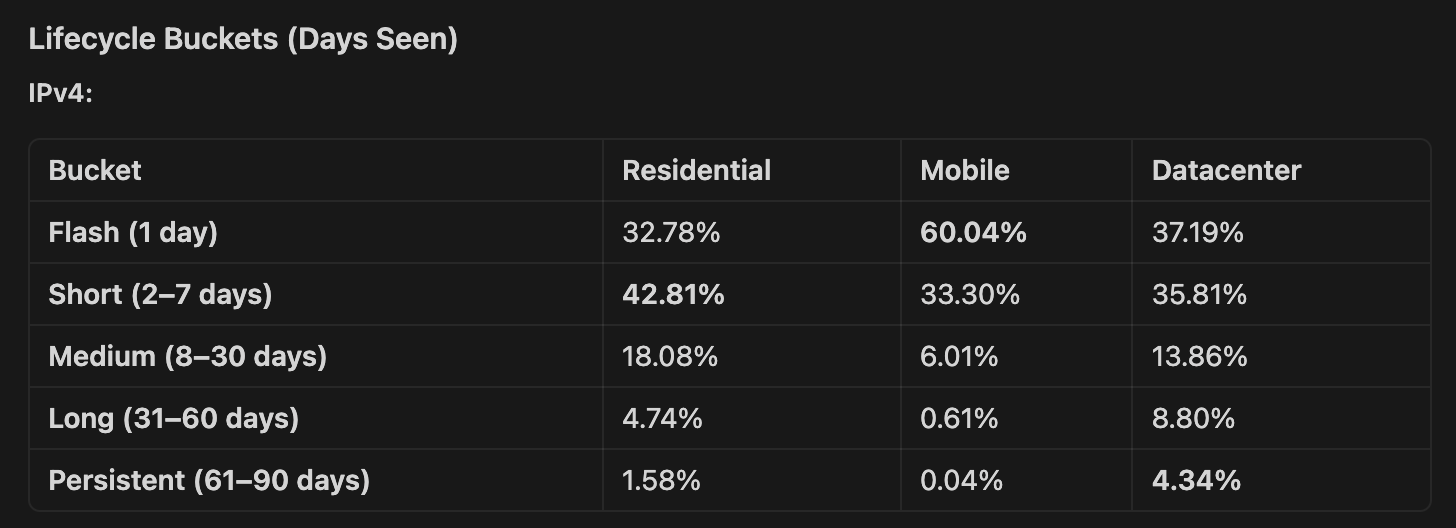
This is infrastructure built for rapid turnover: continuous rotation, broad distribution, and minimal persistence. Across the top residential proxy providers, abuse rates were relatively consistent, generally falling between 17% and 28%, pointing to a structural characteristic of the ecosystem rather than isolated behavior from any single provider.
Read our previous research report on residential proxies.
Different Infrastructure, Different Attack Patterns
The type of infrastructure shapes how it’s used, and we saw clear patterns.
VPNs were more frequently associated with authentication and access-related activity.
Residential proxies were more commonly linked to web scraping, credential stuffing, and application-layer attacks.
What kind of abuse? Web application attacks dominated, appearing in over 61% of abusive IPs overall. Among residential proxy IPs specifically, the top categories were web application attacks (~51%), network and infrastructure attacks (~45%), malware and compromise (~43%), and authentication/access attacks (~42%). VPN IPs showed a similar distribution but with slightly higher representation in authentication-related abuse (~10% of VPN IPs) — consistent with their use in credential-based attacks.

Geographic Distribution Adds Important Context
While the United States had the highest number of abusive IPs overall, proportional analysis highlighted different regions. Countries like Vietnam, Uruguay, and Brazil showed higher concentrations relative to their total IP space.

In some cases, this connects directly to how infrastructure enters the ecosystem.
For example, operators in Brazil described consumer devices, such as IPTV boxes, shipping with embedded residential proxy and botnet functionality. These devices quietly contribute IPs into larger networks.
This expands the footprint of residential proxy infrastructure far beyond traditional data center environments.
Network-Level Patterns
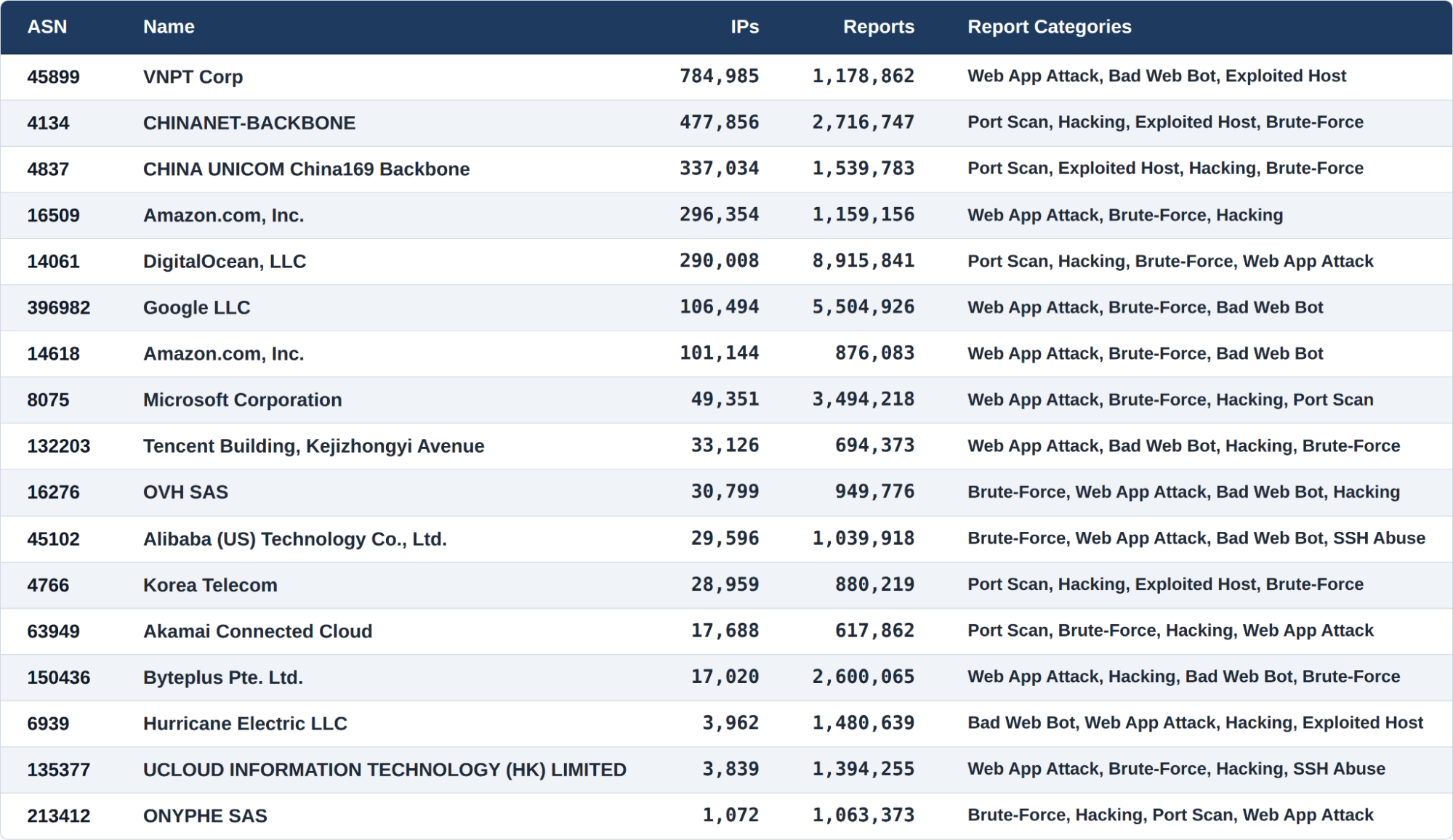
At the ASN level, the most-reported networks were a mix of large Asian ISPs and major cloud providers. The top abusive ASN, VNPT Corp in Vietnam, was also the leading source of residential proxy IPs, reinforcing the connection between residential proxy infrastructure and abuse activity. Cloud providers including Amazon, DigitalOcean, Google, and Microsoft also appeared prominently, with attack types skewing toward web application attacks, brute-force, and port scanning.
Botnets and Residential Proxies Overlap at Scale
To validate the patterns we observed, we analyzed confirmed botnet infrastructure. AbuseIPDB bought access to two botnets to collect the IPs they were using, then we ran them against our data to see what we knew about them.
Of the ~17,000 confirmed botnet IPs, 62% were tagged by IPinfo as VPNs, residential proxies, or both, with the largest share (41%) identified as residential proxies.
This overlap highlights how these systems reinforce each other.
- Botnets can supply IPs into proxy networks
- Proxy networks can extend the reach of botnets
Together, they create a distributed layer of infrastructure that supports both anonymity and scale.
Operationalizing IP Intelligence
Many security workflows still rely on historical reputation, known bad IPs, and static blocklists. That model assumes IP behavior is stable over time, but this research shows a new reality:
- IPs rotate quickly
- Infrastructure shifts continuously
- Abuse signals emerge and disappear in short windows
This is where infrastructure context becomes critical.
AbuseIPDB’s reputation data answers the question: What has this IP done?
IPinfo’s internet infrastructure intelligence answers the question: What is this IP part of? IPinfo can flag these IPs based on infrastructure before they ever appear in abuse databases.
And when combined, AbuseIPDB and IPinfo create a stronger signal that supports earlier detection, better prioritization, and more effective automation.
A Clearer View of Internet Infrastructure
The internet today operates as a dynamic system of overlapping networks, shared infrastructure, and rapidly shifting endpoints.
For teams looking to operationalize these findings, IPinfo and AbuseIPDB both integrate with major SIEM/SOAR platforms, including Splunk, CrowdStrike, Palo Alto, Zscaler, Fortinet, and others. A joint Splunk integration, for example, allows security teams to enrich events with both IP reputation data and residential proxy/VPN classification in a single workflow, powering automated risk scoring and response logic.
The key is combining both signals: AbuseIPDB's reputation data tells you what an IP has done; IPinfo's infrastructure intelligence tells you what that IP is part of. Together, they support earlier detection, better prioritization, and more effective automation especially for the fast-rotating residential proxy infrastructure where historical blocklists alone can't keep up.
VPNs and residential proxies are core parts of that system.
Understanding how they behave, and where they intersect with abuse, helps bring more clarity to how traffic moves and how decisions can be made with greater confidence.
That was the goal of this research at RSAC, to demonstrate how better IP data makes a measurable difference.
About the authors

Daniel Quandt leads the solutions engineering team at IPinfo, where he helps customers get the most out of internet data. Before IPinfo, he worked in data science in the hospitality industry.

Tiago is Head of Anonymizer Detection, where he fine-tunes IP data streaming processes and transforms vast data sets into actionable insights. He was previously a staff research scientist at BitSight Technologies.